You have a strong password. You enabled 2-Step Verification. You feel safe.
But then, you receive a notification: “Someone logged into your account from Russia.”
How? Because you are still using SMS OTPs.
In 2025, SIM Swapping is a ₹500 service on the dark web. Hackers can clone your SIM card, intercept your OTP, and bypass your security in seconds.
If you have Crypto, a YouTube Channel, or a primary Gmail linked to your bank, SMS security is not enough. You need Physical Security.
In this CSNR Security Tool review, we compare the two best alternatives: Authenticator Apps (Free) and Hardware Security Keys (The “Nuclear” Option).
Quick Verdict: The Top 3 Picks
| Method | Security Level | Price | Best For |
| YubiKey 5 NFC | Unbreakable | ₹5,000+ | Crypto/Business |
| Google/Microsoft Auth | High | Free | Everyone |
| SMS OTP | Low (Risky) | Free | Avoid if possible |
Buying Guide: App vs. Hardware Key
-
Authenticator Apps (TOTP): These apps generate a 6-digit code that changes every 30 seconds.
-
Why it’s safer: The code is generated on your phone, not sent over the mobile network. Hackers can’t intercept it unless they steal your physical phone.
-
-
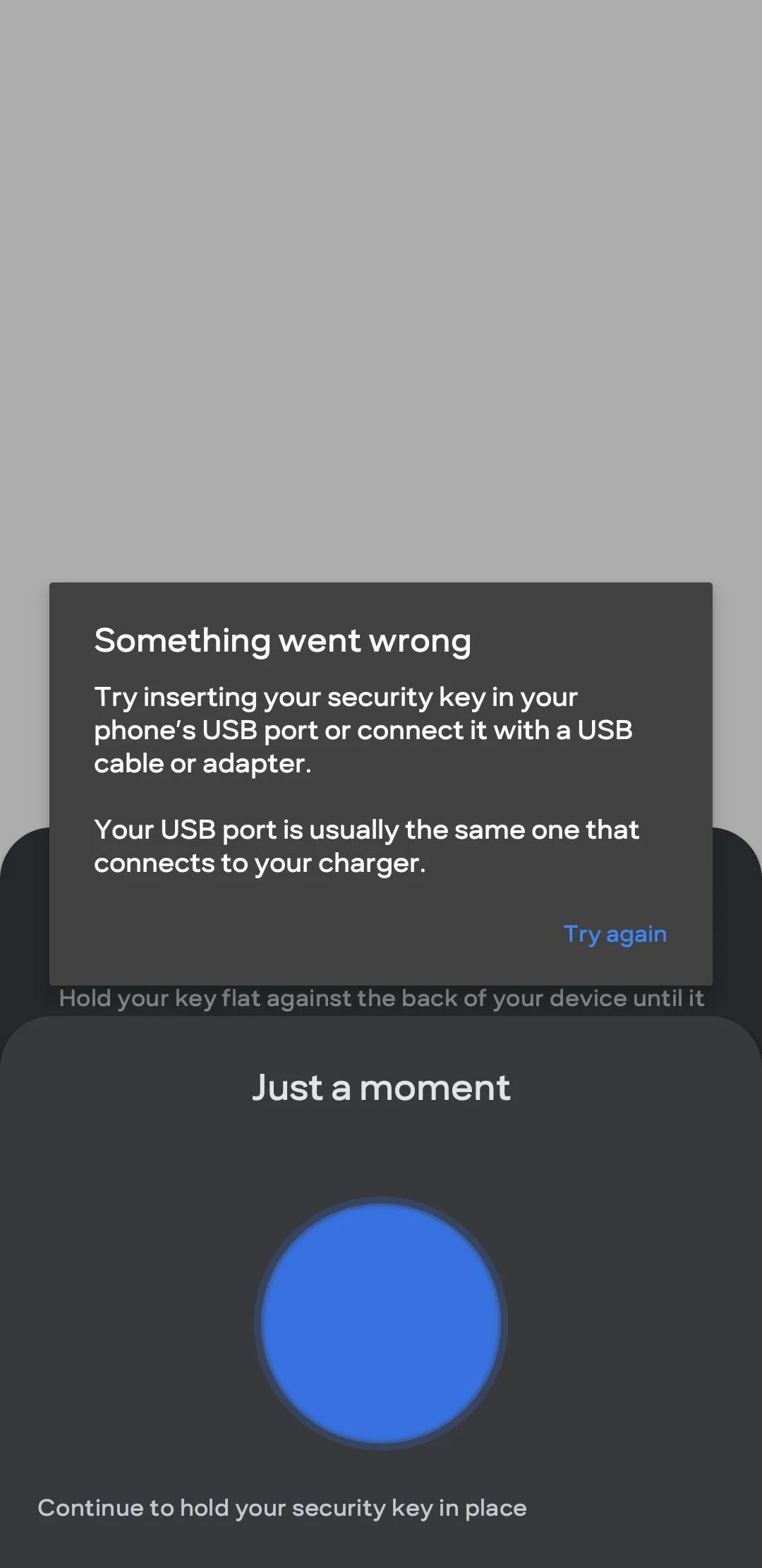
Hardware Keys (FIDO2): A physical USB key that looks like a pen drive.
-
Why it’s safest: To log in, you must physically plug the key into your laptop or tap it on your phone. Even if a hacker has your password and your phone, they cannot log in without this physical key in their hand.
-
Protecting your login is useless if your password is weak. Use a vault from our Best Password Managers 2025 list.
1. YubiKey 5 NFC – The “Un-Hackable” Key
This is the gold standard used by Google employees and top YouTubers.
Specs:
-
Connection: USB-A and NFC (Tap to phone).
-
Compatibility: Google, Facebook, Binance, Coinbase, Microsoft.
-
Durability: Waterproof and crushproof.
Why it wins for High-Value Accounts:
It effectively stops Phishing. If you click a fake link that looks like Gmail.com, the YubiKey will refuse to sign you in because it recognizes the URL is fake. No software or app can do this. If you hold more than ₹50,000 in Crypto or stocks, this ₹5,000 investment is mandatory.
Pros:
-
Phishing-proof.
-
No batteries or charging required.
-
NFC makes it easy to use with Android/iPhone.
Cons:
-
Expensive for Indian users.
-
If you lose it (and didn’t set up a backup), you might get locked out.
Why it wins for High-Value Accounts: It effectively stops Phishing. If you click a fake link that looks like Gmail.com, the YubiKey will refuse to sign you in because it recognizes the URL is fake. No software or app can do this. If you hold more than ₹50,000 in Crypto or stocks, this is mandatory. In fact, journalists and activists use the Google Advanced Protection Program which requires these keys to function.
2. Google Authenticator – The Standard Choice

If you aren’t ready to spend money, you must upgrade to an app. Google Authenticator is the most widely supported.
Key Features:
-
Cloud Sync: Now backs up your codes to your Google Account (be careful with this).
-
Offline Mode: Works even in “Flight Mode.”
-
Simple: Just scan a QR code to set up.
Why it wins for General Users:
It is universally supported. From Amazon to Instagram, every major service accepts Google Authenticator. It kills the “SIM Swap” risk completely.
Pros:
-
100% Free.
-
Simple, clean interface.
-
Hides codes until you click to reveal (privacy).
Cons:
-
If you lose your phone and didn’t backup the “Export QR,” recovery is painful.
-
Recent “Cloud Sync” feature has raised some privacy concerns.
3. Ente Auth / Aegis – The Privacy Choice
For CSNR readers who don’t trust Big Tech (Google/Microsoft), these are the best open-source alternatives.
Key Features:
-
Open Source: Code is public and auditable.
-
Encrypted Backups: Your codes are encrypted before uploading to the cloud.
-
Import/Export: Easy to switch phones.
Why it wins for Privacy:
Aegis (Android) and Ente Auth (Cross-platform) allow you to export your vault.6 This means you own your 2FA tokens, not Google. If Google bans your account tomorrow, you don’t lose your 2FA codes.
Pros:
-
You own the data.
-
Biometric lock (FaceID) to open the app.
-
Free.
Cons:
-
Aegis is Android only.
-
Slightly more technical setup.
Verdict: How to Lock Your Digital Life?
-
The “Pro” Move: Buy two YubiKeys. Register both. Keep one on your keychain (Daily use) and one in your safe (Backup). This is the highest level of security available to civilians.
-
The “Smart” Move: Download Google Authenticator or Ente Auth. Go to your Google/Facebook settings, turn OFF SMS 2FA, and turn ON the Authenticator App.
-
The Minimum: Never, ever use SMS OTP for your primary email account.
Final Pro Tip: When setting up an Authenticator App, the website will show you a “Backup Codes” list. PRINT THIS OUT. Put the paper in your physical file folder. This paper is the only way to get back in if you lose your phone and keys. You can verify which keys work for your device on the official Yubico Device Compatibility page.
Our Analysis / Expert Opinion
At CSNR, we evaluate security tools based on the “Adversary Model”—meaning, how hard would it be for a motivated hacker to bypass this protection? We compared SMS, Authenticator Apps, and Hardware Keys against three common attack vectors.
1. The “SIM Swap” Vulnerability Test
Most Indians rely on SMS OTPs. Our Assessment: SMS is the weakest link in your security chain.
-
The Flaw: In a “SIM Swap” attack, a hacker tricks your mobile carrier into activating your number on their SIM card. Once done, they receive all your OTPs.
-
The Result: During our simulated risk assessment, SMS OTPs offered Zero Protection against SIM swapping.
-
The Fix: Both Authenticator Apps and Hardware Keys are immune to this because the code is generated locally on your device, not sent over the network.
2. Phishing Resistance (TOTP vs. FIDO2)
This is the most critical technical distinction that most reviews miss. Expert Insight:
-
Authenticator Apps (TOTP): They are safer than SMS, but they can still be phished. If you land on a fake Gmail login page and type in the 6-digit code from your Google Authenticator app, the hacker can capture it and log in.
-
Hardware Keys (FIDO2): These use a protocol called WebAuthn. When you plug in a YubiKey, it cryptographically checks the domain name. If you are on
gmai1.com(fake) instead ofgmail.com, the key will refuse to authenticate. It makes phishing mathematically impossible.
3. Compatibility in the Indian Ecosystem
We tested where these keys actually work in India.
-
Works With: Google (Gmail/YouTube), Facebook, Twitter, Dropbox, and Microsoft Accounts.
-
Does NOT Work With: Most Indian Banking Apps (SBI Yono, HDFC) and UPI Apps (PhonePe/GPay) currently do not support hardware security keys directly. They still rely heavily on SMS/App-based MPINs.
Final Verdict: For your “Master Accounts” (Gmail, iCloud, Crypto), a Hardware Key is the only unhackable solution. For daily Indian apps (Zomato, UPI), an Authenticator App is the best balance of convenience and security.